
IT Services for Wealth Managers Done Right: How Retirement Wealth Design Built Compliance-Ready IT Infrastructure in One Week
Alliance Tech Helped a Local St. Louis Wealth Management Firm Achieve Compliance-Ready IT Infrastructure in a Week – Here’s How When Tom Elder opened Retirement[...]
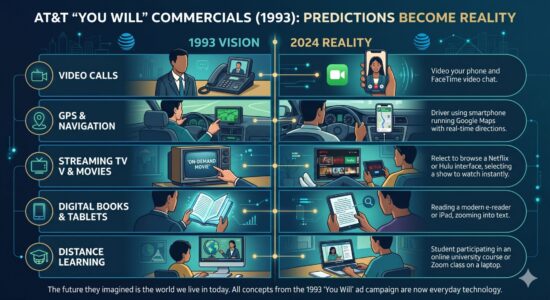
How AT&T’s 1993 Ads Saw the Future
The “You Will” Prophecies: How AT&T’s 1993 Ads Saw the Future In 1993, the internet was a novelty mostly relegated to academic and military institutions.[...]

Microsoft 365 Copilot Updates: What’s New and How Your Team Benefits
Microsoft Copilot 2026: Licensing Changes and New Capabilities Explained Microsoft has streamlined the deployment and functionality of Copilot across the Microsoft 365 ecosystem. These updates[...]

What FINRA’s 2026 AI Guidance Actually Means for St. Louis Financial Services Firms
A Plain-English Breakdown for St. Louis RIAs, Broker-Dealers, and Wealth Managers In December 2025, FINRA published its 2026 Annual Regulatory Oversight Report, a nearly 90-page[...]

The Hidden Gem in Microsoft 365
Why Your Team Should Be Using OneNote Let’s be honest: most team collaboration problems don’t start with a lack of effort. They start with scattered[...]

Stop Wasting the First 10 Minutes of Every Meeting
A Guide to Smarter Conference Rooms A conference room can either sharpen a meeting or quietly derail it. Most businesses have felt both sides of[...]

The End of the “Digital Perimeter”
The End of the “Digital Perimeter”: Why Your Entire Business Needs Zero Trust In the early days of corporate networking, security was often compared to[...]

How to Put Claude AI to Work Immediately
The Small Business Playbook: How to Put Claude AI to Work Immediately For small business owners, time is the most constrained resource. You are the[...]

Decoding Microsoft’s ‘Copilot Code Red’
Decoding Microsoft’s ‘Copilot Code Red’: What It Means for Small Businesses Almost two years after Google declared a company-wide “Code Red” to aggressively pivot toward[...]